Exam Outline Mindmap Summary of Domain 3 LAST MINUTES Read up
Comprehend Cloud Infrastructure Components
-
Physical Environment
- Expensive setup required to run data center to drive cloud services
- The high volume of expensive hardware
- High power densities
- The enormous and immediate impact of downtime
- Multiple levels of service
- Electrical power and cooling pipe
- Ping network connectivity
- Datacenter providers could provide floor space, rack space, cages on any level of aggregation
- Expensive setup required to run data center to drive cloud services
-
Network and Communication
- The purpose of the network is to provide for and control communication between computers— that is, servers and clients.
- Address allocation = Provide Ipadddress
- Access Control = grant or deny access to a resource
- Bandwidth allocation = amount of bandwidth
- Rate limiting = control the number of API Request
- Filtering = allows or denies content or access to resources.
- Routing = Direct the flow of Traffic between endpoint
- The purpose of the network is to provide for and control communication between computers— that is, servers and clients.
-
Compute
- Compute relates to applications and workloads that require a great chance of computation.
- number of CPU
- amount of RAM
- Use of Reservation, Limit, and Share offers the ability for a cloud administrator to allocate the compute resource of a host
- Reservation:
- Reservation is a minimum resource that is guaranteed to a customer
- Limits
- Maximum utilization of the memory process by the customer
- limits are allowed to change dynamically based on current conditions and consumption
- Shares
- resource allocations in case the environment does not have the current capability
- When periods of high utilization and allocation are reached, one point, the system automatically uses each host’s scoring based on its share value to determine which hosts get access to the limited resources still available
- Reservations, limits, and shares are robust resource controls in a virtual environment.
- To understand better follow this link = Source = It very important for exam
- Reservation:
- Compute relates to applications and workloads that require a great chance of computation.
-
Virtualization
- Virtualization abstracts resources from their underlying physical assets
- cloud computing is essentially based on virtualization
- Cloud Computing drives rapid elasticity function via virtualization only
- The cloud the provider will always be responsible for securing the physical infrastructure and the virtualization platform
- Cloud customer is responsible for implementing the
available virtualized security controls and understanding the underlying risks - business cases for using virtualization:
- agile use of hardware
- reduced personnel resourcing
- Offer scalability
- The risk associated with Virtualization
- the flawed hypervisor can facilitate inter-VM attacks
- Network traffic between VMs is not necessarily visible
- Resource availability for VMs can be flawed
- VMs and their disk images are simply files, can be portable and moveable
- Security recommendations for the hypervisor
- Install all updates to the hypervisor as they are released by the vendor.
- Restrict administrative access to the management interfaces of the hypervisor.
- Introspection Capabilities to monitor the security of activity occurring between guest Os. (Very Important for the exam)
- Security recommendations for the guest OS itself:
- Install all updates to the guest OS promptly.
- Back up the virtual drives used by the guest OS on a regular basis, using the same policy for backups
- Good Reference points
-
Storage
-
Management Plane
- The management plane is focused on the management of the environment and all the hosts within it.
- Management plane can be used to do the bulk of the tasks
- Source VMWARE
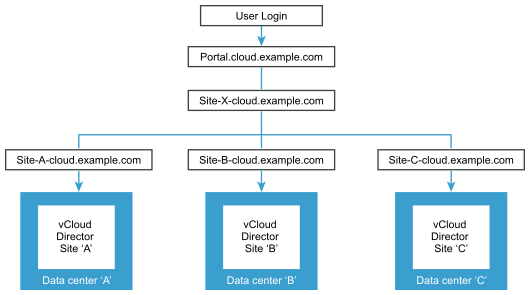
- Getting access to the management plane is like gaining access to your data center unless you put the proper security controls to limit who can access the management plane and what they can do within it
- Access and functions should be tightly audited and reviewed on a regular basis
Design a Secure Data Center
-
Logical Design (e.g., tenant partitioning, access control)
- Source via (AWS
- Each partitioning model takes a very different approach to managing, accessing, and separating tenant data

- Source via (AWS
-
Physical Design (e.g. location, buy or build)
- Organizations can build a data center, buy one, or lease space in a data center
- Regardless of the organization’s decision, certain standards and issues need to be considered and addressed through planning, such as data center tier certification, physical security level, and usage profile
- If you build the data center, the organization has the most control over its design
- significant investment is required to build a robust data center
- When using a shared data center, physical separation of servers and equipment needs to be included in the design.
-
Environmental Design (e.g., Heating, Ventilation and Air Conditioning (HVAC), multi-vendor pathway connectivity)
- adequate conditioning, and backup
- Network connectivity should come from multiple vendors
- ASHRAE
- Low-end temperature = 64.4° F (18° C)
- High-end temperature 80.6° F (27° C)
- Low-end moisture 40% relative humidity and 41.9° F (5.5° C) dew point
- High-end moisture 60% relative humidity and 59° F (15° C) dew point
- HVAC Considerations
- Power for cooling a data center depend on the amount of heat being removed
- Air Management for Data Centers
- Persistent cable management is a key component of effective air management.
- Minimum effective height 24 inches
- Air Managment can reduce operating cost
- Cable Management
- minimize airflow obstruction
- HVAC Design Considerations
-
Risk Assessment and Analysis
- Risk Identification
- Risk Analysis
- Qualitative Risk Analysis
- HIGH,LOW and Medium
- Quantitative Risk Analysis
- SLE.ALE and ARO
- Qualitative Risk Analysis
- Risk Treatment
- Accept the risk = cost of opportunity is higher over risk
- Transfer the risk = financial burden transfer, still risk own by customer
- Avoid the risk = Buisness Decision
- Mitgate risk = implement countermeasure to reduce to an acceptable level
-
Analyze Risks Associated with Cloud Infrastructure
- Cloud Specific Risk
- Policy and Organization Risks
- Provider lock-in
- loss of governance
- Compliance risks
- Provider exit
- General Risks
- Performance issues
- Operability issues
- Integration and protection.
- Consolidation of IT
- Control shift to Cloud Provider
- Virtualization Riskscovered in below point
- Cloud-Specific Risks = Very Important
- Management plane breach
- Resource exhaustion = DOS Attack
- Isolation control failure = one tenant able to access other tenant
- Insecure or incomplete data deletion = Only logical deletion
- Control conflict risk = Shared environment one tenant control impact functionality other tenant
- Software-related risks= Ultimate accountability for compliance still falls to the customer.
- Legal Risks
- Data protection
- Jurisdiction
- Law enforcement
- Licensing
- Non-Cloud- Specific Risks
- Natural disaster
- unauthorized facility
- Policy and Organization Risks
- Cloud Specific Risk
-
Virtualization Risks
- Guest Breakout
- breakout of a guest OS so that it can access the hypervisor. Reason for this attack is flaw in hypervisior
- Snapshot and image security
- portability of image
- Sprwal
- lose control of content because of multiple instance running. Its an administrative issue
- Best book to refer countermeasure Best Practices for Mitigating Risks in Virtualized Environments
- Guest Breakout
-
Counter-measure Strategies
- For Internal control in Data Center Defense in Depth is best answer
- Have compensating control
- Continuous Uptime
- resilient infrastructure
- 99.9999 best to remember for exam
- Automation of Controls
- immediate and comprehensive implementation.
- Access Controls
- Mitigate Multitenant nature of threat in cloud, is by implementing Encrption to achieve confidentiality (Best Answer)
- strong authentication
Design and Plan Security Controls
-
Physical and Environmental Protection (e.g., on-premise
- Datacenter, its buildings, and surroundings.
- Key Regulations to be follow (HIPPA,NERC CIP)
- Protecting Data Center Facilities
- Multiple layers of access controls
- Electricity feeds, network cables, cooling systems, and uninterruptable power supplies (UPSs)
- Redundancy continues in power and network cabling
- Controls on staff include extensive background checks
- Extensive security awareness training
-
System and Communication Protection
- Automation of Configuration
- automation allows for a more granular proliferation of controls.
- faster response to incident
- Responsibilities of Protecting the Cloud System
- IaaS providers typically do not consider guest OS hardening their responsibility.
- Data and GRC is the accountability of Customer in all Service model
- Physical Security is the Accountablity of Provider in all Service Model
- Data Lifecycle
- Data at Rest = Implement encryption
- Data in Motion = VLAN, Multiple zone, mitigate resource contention
- Data in USE = Data in use is protected through secure API calls and web services via the use of encryption, digital signatures
- Automation of Configuration
-
Virtualization Systems Protection
- The virtualization components compute, storage, and network, all governed by the management plane
- Proper alerting and auditing of these actions needs to be considered and governed.
- management plane components are among the highest risk
- Network Security include (IDS,IPS, honeypot)
- The virtualization system components implement controls that isolate tenants
- Trust zone can be defined network segment
- Procedures for snapshotting live images should be incorporated into incident
response procedures to facilitate cloud forensic
-
Identification, Authentication, and Authorization in Cloud Infrastructure
- Managing Identification
- Assertion of Id
- Managing Authentication
- Multifactor is more secure
- Managing Authorization
- In a federated identity model, rely at the relying party.
- Accounting for Resources
- Measures the resources a user consumes during access(billing, trend analysis, resource utilization)
- Managing Identity and Access Management
- Registering, provisioning, and deprovisioning
- Making Access Decisions
- Defining access control matrix
- The Entitlement Process
- Entitlement process starts with business and security requirements and translates these into a set of rules.
- Managing Identification
-
Audit Mechanisms (e.g., log collection, packet capture)
- Cloud Computing Audit Characteristics
- Contract clauses should require transparency
- adequate for the validation of the controls that are important to the consumer
- Audit Improve Transparency and assurance (Exam Point)
- Audit requirements drive by Contracts and SLA
- The Cloud Security Alliance Cloud Controls Matrix
- Facilitate cooperation between cloud service consumers and Cloud Service Provider
- Using a VM
- VM image can be built according to a specified configuration.
- Controls that can be built in a VM image include an automated vulnerability scan start
- Cloud Computing Audit Characteristics
Plan Disaster Recovery (DR) and Business Continuity (BC)
-
Risks Related to the Cloud Environment
-
Business Requirements (e.g., Recovery Time Objective (RTO), Recovery Point Objective (RPO), Recovery Service Level (RSL))
- RSL
- How much computing power need during disaster
- MTD
- Maximum time that the system can be unavailable for Customer
- RPO
- acceptable data loss agreed with client
- RTO
- maximum time take to restore service, should be less then MTD
- WRT
- verify the system and/or data integrity post recovery
- RSL
-
Business Continuity/Disaster Recovery Strategy
- On-Premises, Cloud as BCDR
- Cloud Service provider consider as alternative provider
- Concern
- physical machines need to be converted to workloads in a virtual environment for on premium to cloud transition
- review speed of recovery and test application before migrate (exam point)
- Cloud Service Consumer, Primary Provider BCDR
- When one region or availability zone fails, the service is restored to another part of that same cloud.
- Within one service provider but different availability zone
- load-balancing functionality between zones
- regulatory review for trans border data sharing
- Cloud Service Consumer, Alternative Provider BCDR
- Between two different provider
- same functionality review between two service provider
- portability and interoperability specially in case of SAAS and PAAS
- On-Premises, Cloud as BCDR
-
Creation, Implementation and Testing of Plan
- Scope of the Plan
- Gathering Requirements and Context
- identify critifical business process
- Threat modelling with use case
- Business strategy influences the acceptable RTO and RPO values. (Exam Point)
- BCDR strategy influence external and internal requirements
- Analysis
- Business requirements and the threat model should be analyzed for verification
- Performance requirements (Bandwith and storage(
- Risk Assessment
- All scenarios involve evaluation of the CSP’s capability to deliver
- BCDR will assess for residua risk
- Elasticity feature make CSP availble whenever we need
- contractual terms
- availble bandwidth in which restore services
- All scenarios involve evaluation of the CSP’s capability to deliver
- Design
- evaluate architecture solution
- capture detailed plan who is responsible and accountable for action
- Planning, Exercising, Assessing, and Maintaining the Plan
- testing policy should address testing strategies
- testing strategy includes
- Expectations for business lines and support functions
- details of of testing to be achieved
- People, process and technology involved
- ultimate goal of testing the plan is to ensure that plan should be updated and meeting organization objective (Exam Point)
- Testing Type
- Tabletop Exercise/Structured Walk-Through Test = Update List
- Walk-Through Drill/Simulation Test = Role play
- Functional Drill/Parallel Test = alternate site test
- Full-Interruption/Full-Scale Test =main site testing